AI SOC 2 Type II : How Zero Data Retention Protects Enterprise AI Security
Infron's Enterprise-Grade AI Security Architecture
By Andrew Zheng •
Infron's Enterprise-Grade AI Security Architecture


Feb 9, 2026
Andrew Zheng
In 2025, as artificial intelligence penetrates enterprise core operations, one critical question keeps CTOs and CISOs up at night: How do we ensure AI systems are both powerful and secure?
Key Statistics:
87% of enterprises rank data security as the #1 criterion for AI vendor selection (Gartner 2025)
AI systems process 10-50x more data than traditional software
Every touchpoint—from training datasets to model outputs—presents potential breach risks
Unlike traditional software, AI platforms face unprecedented challenges:
Training data privacy: Preventing unauthorized personal information in datasets
Output reliability: Ensuring AI-generated content is accurate and unbiased
Third-party dependencies: Protecting data across 60+ model providers
Model-specific threats: Adversarial attacks, data leakage, bias amplification
Today's Announcement: Infron AI has successfully completed SOC 2 Type II audit—independent verification of our security commitments over a 6-month observation period.
This guide reveals:
Our zero-trust security architecture from day one
Technical and organizational controls protecting your data
What SOC 2 Type II means for your procurement process
Our roadmap for continuous security improvement
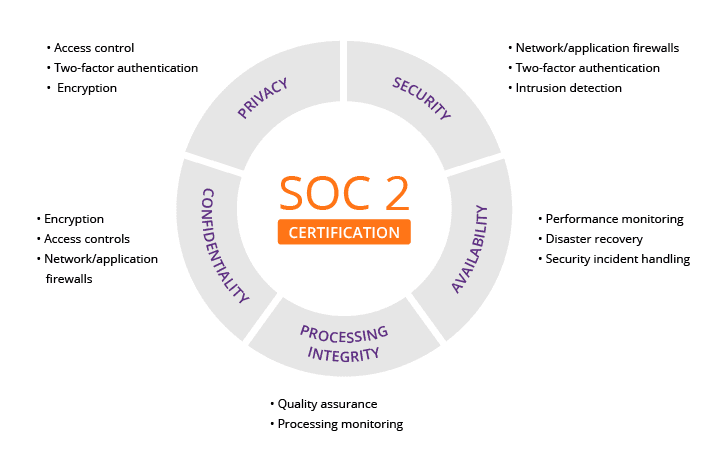
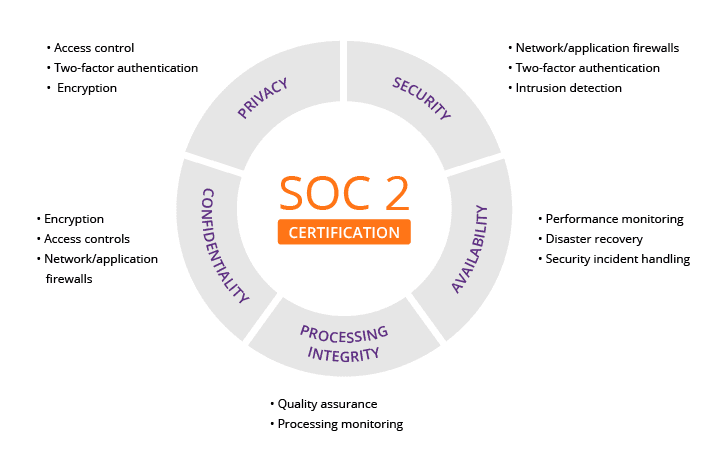
SOC 2 (Service Organization Control 2) is the gold standard audit framework for cloud services, established by the American Institute of Certified Public Accountants (AICPA). Unlike generic standards like ISO 27001, SOC 2 specifically evaluates how SaaS companies manage customer data during service delivery.
Security Criterion | What It Evaluates | AI Platform Challenges |
|---|---|---|
Security | Unauthorized access protection | AI model weights are valuable IP requiring protection |
Availability | System uptime per SLA | High-concurrency, low-latency AI inference requirements |
Processing Integrity | Accurate, complete data processing | Non-deterministic AI model outputs |
Confidentiality | Sensitive data protection | User prompts may contain trade secrets |
Privacy | Personal information handling | Managing PII in training datasets |
Type I (Point-in-time audit):
Validates control design at a single moment
No operational testing
Easier to achieve but less credible
Type II (Continuous audit):
✅ Requires minimum 6-month observation period
✅ Tests if controls actually work in production
✅ Proves long-term commitment, not one-time effort
✅ Preferred by enterprise procurement teams
Our Audit Scope (May-November 2025):
3 on-site audits
47 control tests
200+ evidence documents reviewed
Zero exceptions or deficiencies
Traditional SaaS focuses on storage and transmission security. AI platforms face additional layers:
1. Model Lifecycle Security
Data collection → Training → Validation → Deployment → Monitoring
Each stage requires specialized controls
2. Third-Party Model Dependencies
As an AI Model Router, Infron AI integrates:
OpenAI, Anthropic, Google Gemini, Meta Llama
60+ total model providers
Challenge: Ensuring end-to-end data protection across all vendors
3. Dynamic Data Flows
Requests traverse multiple models in milliseconds
Must protect data without sacrificing performance
4. AI-Specific Threats
Model poisoning (adversarial attacks)
Training data leakage
Bias amplification
Prompt injection attacks
"Privacy by Design" isn't marketing—it's our engineering philosophy. Data protection is architected in, not bolted on.
All API traffic encrypted with TLS 1.3:
Advantages over TLS 1.2:
⚡ Reduced handshake latency
🔒 Removed insecure ciphers (RC4, 3DES)
🛡️ Mandatory Forward Secrecy (historical communications safe even if keys leak)
Implementation: API endpoints reject connections using protocols older than TLS 1.3.
For temporarily stored data (active request queues):
Encryption Standard: AES-256 (industry-leading symmetric encryption)
Hierarchical Key Management:
Security Benefit: Even if one layer is compromised, data remains protected.
The Promise: Your data is never used for training, never stored for analysis, never shared with third parties.
How It Works:
⏱️ 5-second purge: All request data deleted within 5 seconds post-processing
📊 Metadata-only logs: We record request time, status codes, token usage—never prompts or outputs
✅ SOC 2 verified: Auditors validated our data lifecycle management
Competitive Advantage: Unlike platforms that train on user data, your trade secrets never persist in our systems.
Role-Based Access Control (RBAC):
Developers: No production data access
Operations: System logs only
Security: Audit permissions for incident response
Multi-Factor Authentication (MFA):
Mandatory hardware keys (YubiKey) or biometrics
IP whitelisting for API keys
Just-In-Time (JIT) Access:
Temporary permissions (1-4 hours) via manager-approved tickets
Full audit trail for every operation
Regular Reviews:
Quarterly company-wide permission audits
Auto-revoke unused access after 90 days
Immediate revocation upon employee departure
Perimeter Protection:
WAF: Blocks SQL injection, XSS attacks
DDoS Protection: Withstands 100+ Gbps attacks (via Cloudflare)
Rate Limiting: Prevents API abuse
Network Segmentation:
Intrusion Detection (IDS/IPS):
Real-time anomaly monitoring
Automatic suspicious IP blocking
Threat intelligence integration
1. Training Data Governance
✅ Only anonymized performance metrics (latency, success rates)
✅ Zero user content in training datasets
✅ Full data provenance tracking
2. Model Version Control Every algorithm update follows:
Development environment testing
A/B testing (5% traffic initially)
Security team review
Multi-level approval
5-minute rollback capability
3. Third-Party Model Risk Management
Vendor Tier System:
Tier 1 (Critical): SOC 2 required, annual audits (OpenAI, Anthropic)
Tier 2 (Important): Security questionnaires, signed DPAs
Tier 3 (General): Standard contract protections
Vendor Risk Dashboard tracks:
Certification status (SOC 2, ISO 27001)
Data processing locations
Security incident history
Contract expiration dates
Contract Protections:
🚫 Zero data training clause
🗑️ Immediate data deletion requirements
🔍 Audit rights reserved
Our Commitments:
Route based on client criteria (cost/speed/quality)
Deliver requests successfully or report clear errors
Return complete outputs without tampering
Verification Mechanisms:
Traceable routing decision logs
End-to-end checksums
Daily automated testing
Quality Monitoring:
Input validation (format checks, content filtering)
Output anomaly detection (garbled text, unusual patterns)
Latency tracking with automatic failover
99%+ success rate threshold
Model Drift Detection:
Daily benchmark test suites
User feedback trend analysis
Automatic degradation of underperforming models
Bias & Fairness Reviews:
Diversity testing across demographic groups
Service quality consistency monitoring
Transparent routing algorithm documentation
Executive Leadership:
CEO (ultimate accountability)
CTO (technical decisions)
CISO (security oversight)
Legal Lead (compliance)
Product Lead (privacy impact assessments)
Responsibilities:
Quarterly risk reviews
Policy updates for regulatory changes
Incident response coordination
Security budget allocation
Triggers:
New product/feature launch
Processing new data types
Changing vendors or storage locations
Assessment Framework:
Data Mapping: What/where/who/how long?
Risk Assessment: Breach impact, sensitivity, cross-border transfers
Mitigation: Technical controls, user consent, deletion procedures
Approval: Accept/mitigate/reject decision
Case Study: Enterprise SSO Integration PIA
Risk Identified: Potential IdP access point for attackers
Mitigations Implemented:
SAML 2.0/OAuth 2.0 (no credential storage)
Strict rate limiting
Customer IP whitelisting
Regular penetration testing
Result: Approved after risk reduction
1. Onboarding (Week 1)
Data privacy fundamentals
Phishing/social engineering recognition
Secure coding practices
Incident reporting procedures
Required: 80% passing score on online test
2. Annual Refresher Training
Previous year's security incidents
Emerging threats (AI-driven phishing)
Policy updates (new regulations)
3. Role-Specific Training
Role | Specialized Content |
|---|---|
Engineers | OWASP Top 10, key management, code review |
Data Scientists | Anonymization, bias detection, responsible AI |
Customer Support | Data deletion requests, escalation procedures |
Sales | Safe SOC 2 sharing, avoiding over-promises |
4. Simulation Drills
Quarterly phishing email tests
Annual data breach tabletop exercises
Social engineering penetration tests
5. Security Culture Building
Privacy Champions in each team
Bug bounty rewards
No-blame reporting policy
Executive role modeling
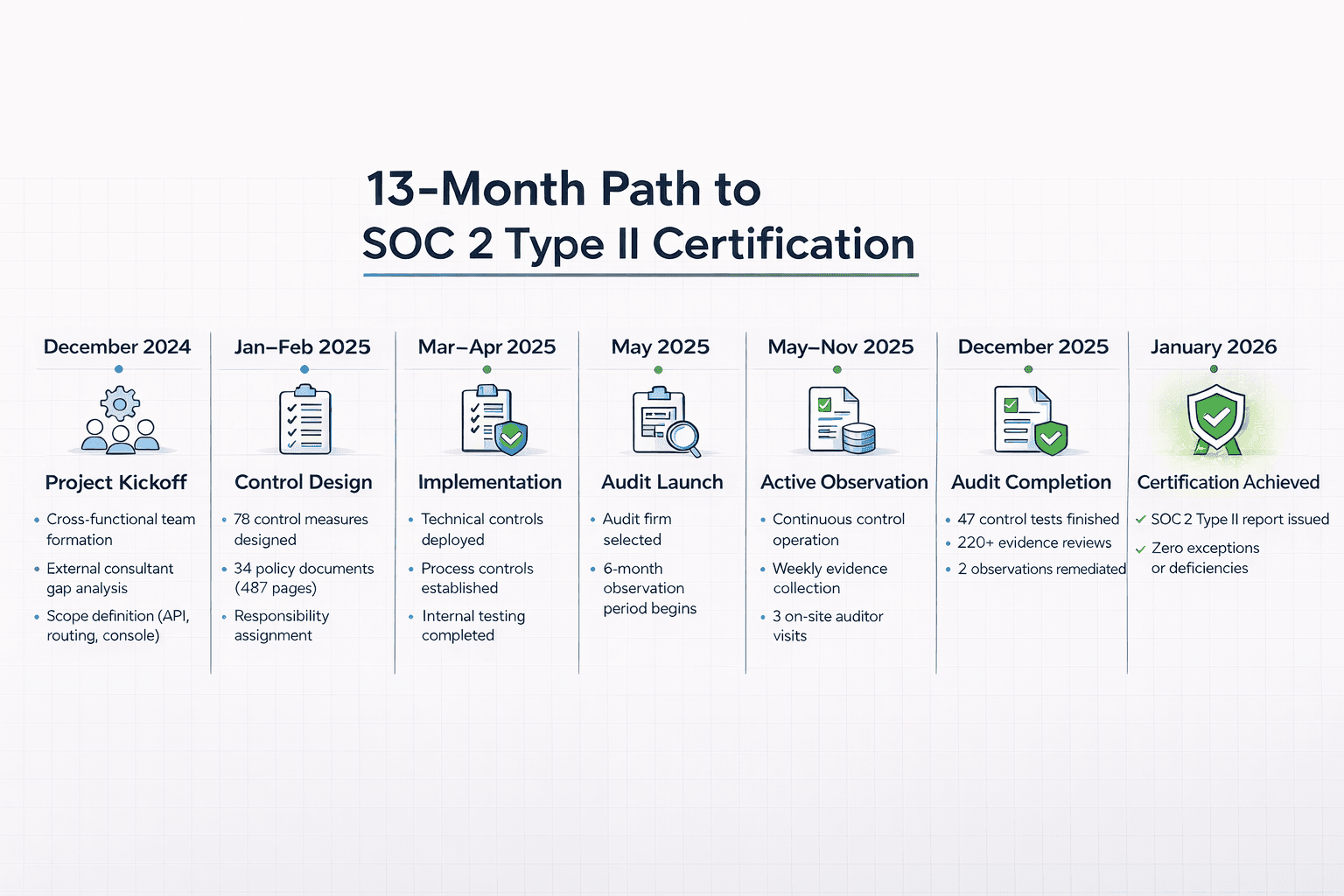
December 2024: Project Kickoff
Cross-functional team formation
External consultant gap analysis
Scope definition (API, routing, console)
January-February 2025: Control Design
78 control measures designed
34 policy documents (487 pages)
Responsibility assignment
March-April 2025: Implementation
Technical controls deployed
Process controls established
Internal testing completed
May 2025: Audit Launch
Audit firm selected
6-month observation period begins
May-November 2025: Active Observation
Continuous control operation
Weekly evidence collection
3 on-site auditor visits
December 2025: Audit Completion
47 control tests finished
220+ evidence reviews
2 observations remediated
January 2026: Certification Achieved
✅ SOC 2 Type II report issued
✅ Zero exceptions or deficiencies
Challenge: Traditional logging conflicts with privacy commitments
Solution:
Metadata-only logging system
Real-time debugging tools (user-authorized)
Structured error codes for troubleshooting
Outcome: Became our strongest competitive differentiator
Challenge: Managing 60+ model provider risks
Solution:
Three-tier vendor classification
Real-time risk dashboard
Comprehensive contract protections
Outcome: Auditors praised our vendor management maturity
Challenge: Proving "integrity" for probabilistic outputs
Solution:
Clearly defined processing commitments
Traceable routing decision logs
Daily automated verification testing
Outcome: Set industry precedent for AI interpretation
Observation 1: Inconsistent log retention (90 vs 120 days)
Remediation: Unified configuration, automated compliance checks
Observation 2: 3 employees missed training deadline (4%)
Remediation: Three-tier reminder system, automatic access suspension
Resolution: Both fixed within 30 days, zero impact on certification
Traditional Vendor Review (3-6 months):
100+ question security questionnaires
Architecture diagram reviews
On-site security audits
Legal DPA negotiations
With SOC 2 Type II (3-6 weeks):
✅ Pre-filled standard questionnaires (SIG, CAIQ, VSA)
✅ Complete report under NDA
✅ Accepted by most enterprise security teams
✅ Fast-track approval process
Real Case Study: Fortune 500 financial institution
Before: 4-month review cycle
After: 6-week approval with SOC 2 report
Result: Project launched 2.5 months early
Regulatory Alignment:
GDPR Article 28: SOC 2 proves "sufficient guarantees"
CCPA: Demonstrates vendor due diligence
Industry Standards: Meets banking, healthcare, government requirements
Risk Mitigation:
Transfer audit burden to third-party verification
Reduce regulatory fine exposure
Demonstrate supply chain security
Unlike competitors who retain data for "improvement":
Scenario | Data-Retaining Platform | Infron AI (ZDR) |
|---|---|---|
Law Firm Contracts | Trade secrets at risk of competitor access | 5-second deletion, zero leakage risk |
Customer Contracts | May violate "no third-party training" clauses | ZDR aligns with contractual obligations |
Privacy Assessments | High risk scores from data retention | Significantly lower risk profile |
Ongoing Assurance:
Annual re-audits
Real-time compliance monitoring
Proactive change notifications
Transparency Options:
Request full SOC 2 report ([email protected])
Annual security review meetings with CISO
Direct communication channel for concerns
ISO 27001 (June 2026 target)
HIPAA Compliance for healthcare customers
FedRAMP readiness for government agencies
Customer-Managed Encryption Keys (CMEK):
Your keys = your control
Infron cannot decrypt without your permission
Dedicated VPC Deployment:
Physically isolated instances
Data never leaves your cloud
Data Localization:
Choose processing region (US/EU/APAC)
Meet data residency requirements
Model Security: Prompt injection defense, content watermarking
Zero-Knowledge Proofs: Process requests without seeing data
Industry Leadership: Open-source tools, standards participation
Our Commitments:
🔓 Open-source security tools
📚 Share best practices publicly
🤝 Participate in standards development (NIST, ISO)
🔍 Responsible vulnerability disclosure
In the AI era, trust is the scarcest resource. Enterprises need partners who:
❌ Won't commoditize your data
❌ Won't compromise on security
❌ Won't abandon principles under pressure
✅ Verified Security: 6 months of audited operational controls
✅ Architectural Privacy: Built-in protection, not afterthought
✅ Zero Data Retention: Independently verified deletion practices
✅ Continuous Excellence: Annual re-certification commitment
Choose Infron for:
🔌 Access to 300+ AI models
⚡ 99.9% availability SLA
💰 35% average cost savings
🛡️ Partner who treats your data security as sacred
Learn more: How Infron gives you control over your data
Request SOC 2 Report: [email protected]
Book Security Review and Start Free Trial: Contact Us
Experience enterprise-grade AI security today!
In 2025, as artificial intelligence penetrates enterprise core operations, one critical question keeps CTOs and CISOs up at night: How do we ensure AI systems are both powerful and secure?
Key Statistics:
87% of enterprises rank data security as the #1 criterion for AI vendor selection (Gartner 2025)
AI systems process 10-50x more data than traditional software
Every touchpoint—from training datasets to model outputs—presents potential breach risks
Unlike traditional software, AI platforms face unprecedented challenges:
Training data privacy: Preventing unauthorized personal information in datasets
Output reliability: Ensuring AI-generated content is accurate and unbiased
Third-party dependencies: Protecting data across 60+ model providers
Model-specific threats: Adversarial attacks, data leakage, bias amplification
Today's Announcement: Infron AI has successfully completed SOC 2 Type II audit—independent verification of our security commitments over a 6-month observation period.
This guide reveals:
Our zero-trust security architecture from day one
Technical and organizational controls protecting your data
What SOC 2 Type II means for your procurement process
Our roadmap for continuous security improvement
SOC 2 (Service Organization Control 2) is the gold standard audit framework for cloud services, established by the American Institute of Certified Public Accountants (AICPA). Unlike generic standards like ISO 27001, SOC 2 specifically evaluates how SaaS companies manage customer data during service delivery.
Security Criterion | What It Evaluates | AI Platform Challenges |
|---|---|---|
Security | Unauthorized access protection | AI model weights are valuable IP requiring protection |
Availability | System uptime per SLA | High-concurrency, low-latency AI inference requirements |
Processing Integrity | Accurate, complete data processing | Non-deterministic AI model outputs |
Confidentiality | Sensitive data protection | User prompts may contain trade secrets |
Privacy | Personal information handling | Managing PII in training datasets |
Type I (Point-in-time audit):
Validates control design at a single moment
No operational testing
Easier to achieve but less credible
Type II (Continuous audit):
✅ Requires minimum 6-month observation period
✅ Tests if controls actually work in production
✅ Proves long-term commitment, not one-time effort
✅ Preferred by enterprise procurement teams
Our Audit Scope (May-November 2025):
3 on-site audits
47 control tests
200+ evidence documents reviewed
Zero exceptions or deficiencies
Traditional SaaS focuses on storage and transmission security. AI platforms face additional layers:
1. Model Lifecycle Security
Data collection → Training → Validation → Deployment → Monitoring
Each stage requires specialized controls
2. Third-Party Model Dependencies
As an AI Model Router, Infron AI integrates:
OpenAI, Anthropic, Google Gemini, Meta Llama
60+ total model providers
Challenge: Ensuring end-to-end data protection across all vendors
3. Dynamic Data Flows
Requests traverse multiple models in milliseconds
Must protect data without sacrificing performance
4. AI-Specific Threats
Model poisoning (adversarial attacks)
Training data leakage
Bias amplification
Prompt injection attacks
"Privacy by Design" isn't marketing—it's our engineering philosophy. Data protection is architected in, not bolted on.
All API traffic encrypted with TLS 1.3:
Advantages over TLS 1.2:
⚡ Reduced handshake latency
🔒 Removed insecure ciphers (RC4, 3DES)
🛡️ Mandatory Forward Secrecy (historical communications safe even if keys leak)
Implementation: API endpoints reject connections using protocols older than TLS 1.3.
For temporarily stored data (active request queues):
Encryption Standard: AES-256 (industry-leading symmetric encryption)
Hierarchical Key Management:
Security Benefit: Even if one layer is compromised, data remains protected.
The Promise: Your data is never used for training, never stored for analysis, never shared with third parties.
How It Works:
⏱️ 5-second purge: All request data deleted within 5 seconds post-processing
📊 Metadata-only logs: We record request time, status codes, token usage—never prompts or outputs
✅ SOC 2 verified: Auditors validated our data lifecycle management
Competitive Advantage: Unlike platforms that train on user data, your trade secrets never persist in our systems.
Role-Based Access Control (RBAC):
Developers: No production data access
Operations: System logs only
Security: Audit permissions for incident response
Multi-Factor Authentication (MFA):
Mandatory hardware keys (YubiKey) or biometrics
IP whitelisting for API keys
Just-In-Time (JIT) Access:
Temporary permissions (1-4 hours) via manager-approved tickets
Full audit trail for every operation
Regular Reviews:
Quarterly company-wide permission audits
Auto-revoke unused access after 90 days
Immediate revocation upon employee departure
Perimeter Protection:
WAF: Blocks SQL injection, XSS attacks
DDoS Protection: Withstands 100+ Gbps attacks (via Cloudflare)
Rate Limiting: Prevents API abuse
Network Segmentation:
Intrusion Detection (IDS/IPS):
Real-time anomaly monitoring
Automatic suspicious IP blocking
Threat intelligence integration
1. Training Data Governance
✅ Only anonymized performance metrics (latency, success rates)
✅ Zero user content in training datasets
✅ Full data provenance tracking
2. Model Version Control Every algorithm update follows:
Development environment testing
A/B testing (5% traffic initially)
Security team review
Multi-level approval
5-minute rollback capability
3. Third-Party Model Risk Management
Vendor Tier System:
Tier 1 (Critical): SOC 2 required, annual audits (OpenAI, Anthropic)
Tier 2 (Important): Security questionnaires, signed DPAs
Tier 3 (General): Standard contract protections
Vendor Risk Dashboard tracks:
Certification status (SOC 2, ISO 27001)
Data processing locations
Security incident history
Contract expiration dates
Contract Protections:
🚫 Zero data training clause
🗑️ Immediate data deletion requirements
🔍 Audit rights reserved
Our Commitments:
Route based on client criteria (cost/speed/quality)
Deliver requests successfully or report clear errors
Return complete outputs without tampering
Verification Mechanisms:
Traceable routing decision logs
End-to-end checksums
Daily automated testing
Quality Monitoring:
Input validation (format checks, content filtering)
Output anomaly detection (garbled text, unusual patterns)
Latency tracking with automatic failover
99%+ success rate threshold
Model Drift Detection:
Daily benchmark test suites
User feedback trend analysis
Automatic degradation of underperforming models
Bias & Fairness Reviews:
Diversity testing across demographic groups
Service quality consistency monitoring
Transparent routing algorithm documentation
Executive Leadership:
CEO (ultimate accountability)
CTO (technical decisions)
CISO (security oversight)
Legal Lead (compliance)
Product Lead (privacy impact assessments)
Responsibilities:
Quarterly risk reviews
Policy updates for regulatory changes
Incident response coordination
Security budget allocation
Triggers:
New product/feature launch
Processing new data types
Changing vendors or storage locations
Assessment Framework:
Data Mapping: What/where/who/how long?
Risk Assessment: Breach impact, sensitivity, cross-border transfers
Mitigation: Technical controls, user consent, deletion procedures
Approval: Accept/mitigate/reject decision
Case Study: Enterprise SSO Integration PIA
Risk Identified: Potential IdP access point for attackers
Mitigations Implemented:
SAML 2.0/OAuth 2.0 (no credential storage)
Strict rate limiting
Customer IP whitelisting
Regular penetration testing
Result: Approved after risk reduction
1. Onboarding (Week 1)
Data privacy fundamentals
Phishing/social engineering recognition
Secure coding practices
Incident reporting procedures
Required: 80% passing score on online test
2. Annual Refresher Training
Previous year's security incidents
Emerging threats (AI-driven phishing)
Policy updates (new regulations)
3. Role-Specific Training
Role | Specialized Content |
|---|---|
Engineers | OWASP Top 10, key management, code review |
Data Scientists | Anonymization, bias detection, responsible AI |
Customer Support | Data deletion requests, escalation procedures |
Sales | Safe SOC 2 sharing, avoiding over-promises |
4. Simulation Drills
Quarterly phishing email tests
Annual data breach tabletop exercises
Social engineering penetration tests
5. Security Culture Building
Privacy Champions in each team
Bug bounty rewards
No-blame reporting policy
Executive role modeling
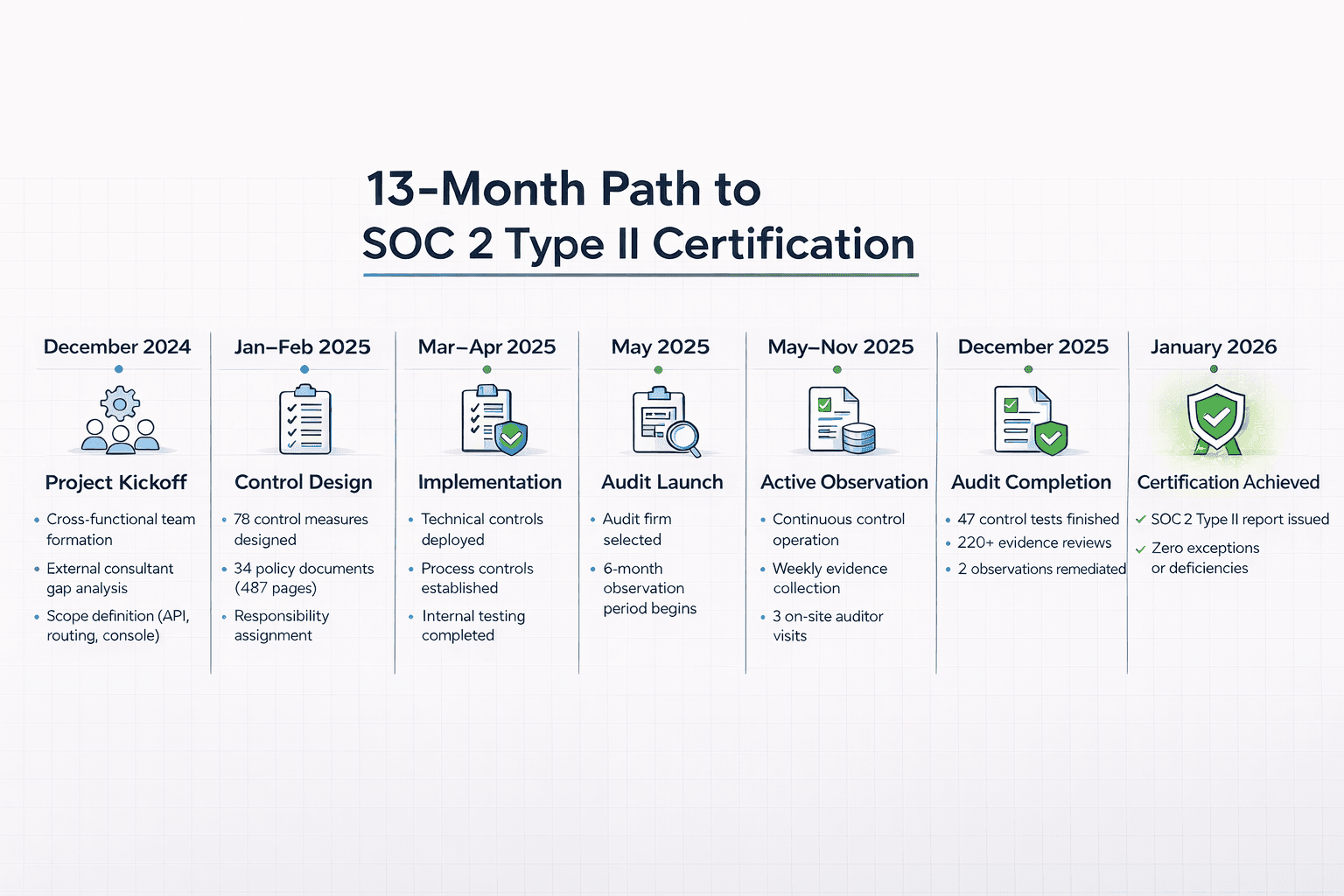
December 2024: Project Kickoff
Cross-functional team formation
External consultant gap analysis
Scope definition (API, routing, console)
January-February 2025: Control Design
78 control measures designed
34 policy documents (487 pages)
Responsibility assignment
March-April 2025: Implementation
Technical controls deployed
Process controls established
Internal testing completed
May 2025: Audit Launch
Audit firm selected
6-month observation period begins
May-November 2025: Active Observation
Continuous control operation
Weekly evidence collection
3 on-site auditor visits
December 2025: Audit Completion
47 control tests finished
220+ evidence reviews
2 observations remediated
January 2026: Certification Achieved
✅ SOC 2 Type II report issued
✅ Zero exceptions or deficiencies
Challenge: Traditional logging conflicts with privacy commitments
Solution:
Metadata-only logging system
Real-time debugging tools (user-authorized)
Structured error codes for troubleshooting
Outcome: Became our strongest competitive differentiator
Challenge: Managing 60+ model provider risks
Solution:
Three-tier vendor classification
Real-time risk dashboard
Comprehensive contract protections
Outcome: Auditors praised our vendor management maturity
Challenge: Proving "integrity" for probabilistic outputs
Solution:
Clearly defined processing commitments
Traceable routing decision logs
Daily automated verification testing
Outcome: Set industry precedent for AI interpretation
Observation 1: Inconsistent log retention (90 vs 120 days)
Remediation: Unified configuration, automated compliance checks
Observation 2: 3 employees missed training deadline (4%)
Remediation: Three-tier reminder system, automatic access suspension
Resolution: Both fixed within 30 days, zero impact on certification
Traditional Vendor Review (3-6 months):
100+ question security questionnaires
Architecture diagram reviews
On-site security audits
Legal DPA negotiations
With SOC 2 Type II (3-6 weeks):
✅ Pre-filled standard questionnaires (SIG, CAIQ, VSA)
✅ Complete report under NDA
✅ Accepted by most enterprise security teams
✅ Fast-track approval process
Real Case Study: Fortune 500 financial institution
Before: 4-month review cycle
After: 6-week approval with SOC 2 report
Result: Project launched 2.5 months early
Regulatory Alignment:
GDPR Article 28: SOC 2 proves "sufficient guarantees"
CCPA: Demonstrates vendor due diligence
Industry Standards: Meets banking, healthcare, government requirements
Risk Mitigation:
Transfer audit burden to third-party verification
Reduce regulatory fine exposure
Demonstrate supply chain security
Unlike competitors who retain data for "improvement":
Scenario | Data-Retaining Platform | Infron AI (ZDR) |
|---|---|---|
Law Firm Contracts | Trade secrets at risk of competitor access | 5-second deletion, zero leakage risk |
Customer Contracts | May violate "no third-party training" clauses | ZDR aligns with contractual obligations |
Privacy Assessments | High risk scores from data retention | Significantly lower risk profile |
Ongoing Assurance:
Annual re-audits
Real-time compliance monitoring
Proactive change notifications
Transparency Options:
Request full SOC 2 report ([email protected])
Annual security review meetings with CISO
Direct communication channel for concerns
ISO 27001 (June 2026 target)
HIPAA Compliance for healthcare customers
FedRAMP readiness for government agencies
Customer-Managed Encryption Keys (CMEK):
Your keys = your control
Infron cannot decrypt without your permission
Dedicated VPC Deployment:
Physically isolated instances
Data never leaves your cloud
Data Localization:
Choose processing region (US/EU/APAC)
Meet data residency requirements
Model Security: Prompt injection defense, content watermarking
Zero-Knowledge Proofs: Process requests without seeing data
Industry Leadership: Open-source tools, standards participation
Our Commitments:
🔓 Open-source security tools
📚 Share best practices publicly
🤝 Participate in standards development (NIST, ISO)
🔍 Responsible vulnerability disclosure
In the AI era, trust is the scarcest resource. Enterprises need partners who:
❌ Won't commoditize your data
❌ Won't compromise on security
❌ Won't abandon principles under pressure
✅ Verified Security: 6 months of audited operational controls
✅ Architectural Privacy: Built-in protection, not afterthought
✅ Zero Data Retention: Independently verified deletion practices
✅ Continuous Excellence: Annual re-certification commitment
Choose Infron for:
🔌 Access to 300+ AI models
⚡ 99.9% availability SLA
💰 35% average cost savings
🛡️ Partner who treats your data security as sacred
Learn more: How Infron gives you control over your data
Request SOC 2 Report: [email protected]
Book Security Review and Start Free Trial: Contact Us
Experience enterprise-grade AI security today!
Infron's Enterprise-Grade AI Security Architecture
By Andrew Zheng •

LLM gateways

LLM gateways

A Technical Roadmap for R&D Teams

A Technical Roadmap for R&D Teams
Infron's multi-provider security architecture
Infron's multi-provider security architecture
Seamlessly integrate Infron with just a few lines of code and unlock unlimited AI power.

Seamlessly integrate Infron with just a few lines of code and unlock unlimited AI power.

Seamlessly integrate Infron with just a few lines of code and unlock unlimited AI power.
